Information Security
Government Cell Phone Tracking: Domestic Surveillance
The right to privacy is being challenged by various forms of surveillance today. Cell phones are the repositories of abundant personal information and the government is listening.
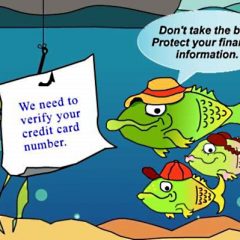
4 Common Technology Scams And How To Avoid Them
Technology scams are becoming more and more common and much cleverer in the way they target us. Here are four f the most common cons and how to prevent them.
Can Your Data Cloud Weather The Storm?
As safe as cloud technology is supposed to be, you should still be aware that this technology comes with notable risks.
Programmers Needn’t Be Nervous That The Software They Create Can Be Reverse Engineered
IT has helped companies become more streamlined and increase productivity, but along with the pros of IT, a host of risks and uncertainties have emerged.